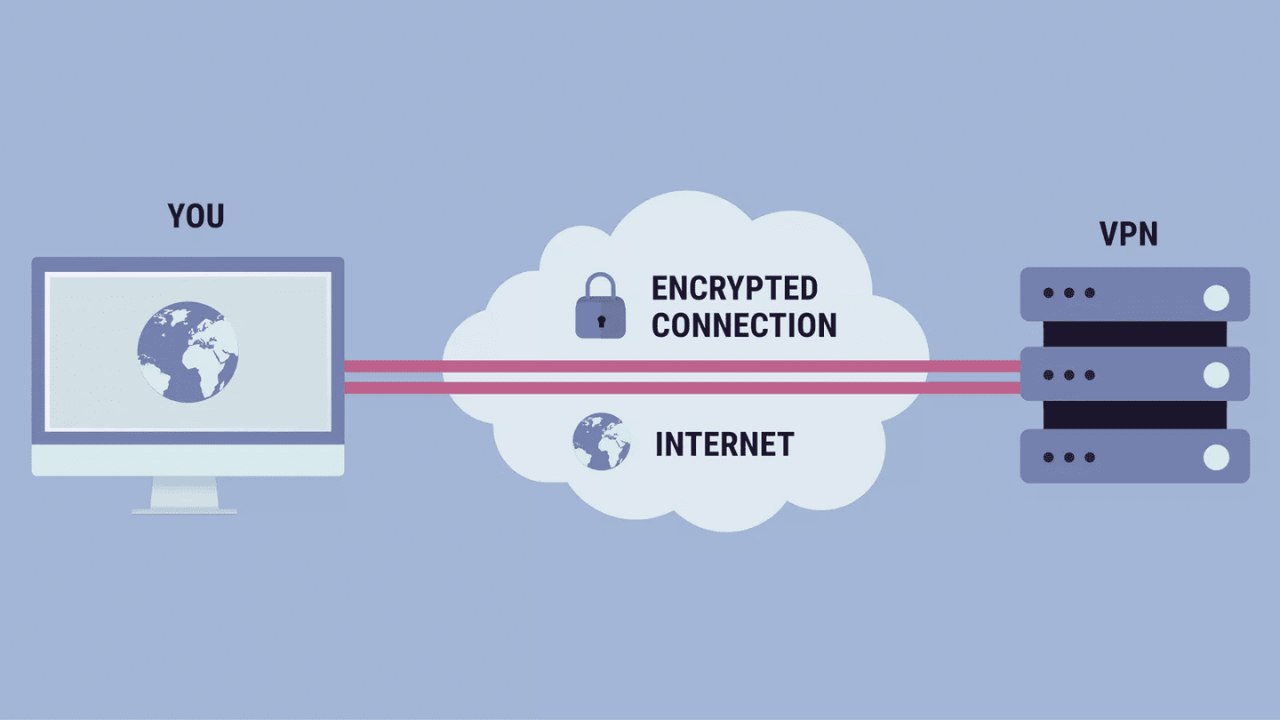
As concerns about online privacy, data security, and unrestricted internet access continue to grow, Virtual Private Networks (VPNs) have become a common solution. However, they are not the only option available. A range of emerging technologies and alternative tools now offer different ways to secure connections, enhance privacy, or bypass restrictions, often with unique advantages.




No comments yet. Be the first to share your thoughts!